An ‘Encrypted’ Encryptor Menaces Gamers: TeslaCrypt 2.0 Conceals its Identity to Demand a $500 Ransom
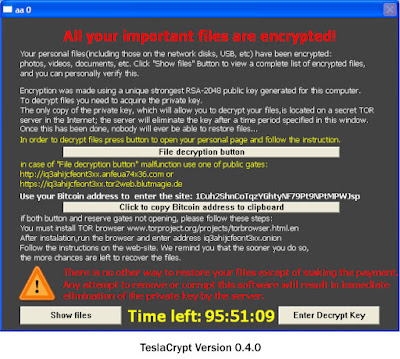
Kaspersky Lab has detected a curious behavior in a new threat from the TeslaCrypt ransomware encryptor family. In version 2.0 of the Trojan, notorious for infecting computer gamers, it displays an HTML page in the web browser which is an exact copy of CryptoWall 3.0, another notorious ransomware program.
Perhaps the criminals are doing this as a statement of intent. So far, many files encrypted by CryptoWall could not be decrypted, which is not the case with many past cases of TeslaCrypt infection. After a successful infection, the malicious program demands a $500 (more than PhP20,000) ransom for the decryption key. If the victim delays, the ransom doubles.
Ransomware is a type of malware used as a digital mechanism for extortion. It is a type of software to block access to a computer system until a ransom is paid.
Early samples of TeslaCrypt were detected in February 2015 and the new ransomware Trojan gained immediate notoriety as a menace to computer gamers. Amongst other types of target files, it tries to infect typical gaming files: game saves, user profiles, recorded replays etc. That said, TeslaCrypt does not encrypt files that are larger than 268 MB.
Most TeslaCrypt infections occur in the USA, Germany and Spain, followed by Italy, France and United Kingdom.

In a related report from Threat Post, they quoted Bleeping Computer which reported that “50 different types of files associated with popular games like MineCraft, Call of Duty, and World of Warcraft were some of the first to be targeted.” The computer help site also said that TeslaCrypt “pays peculiar attention” to other popular games like Dragon Age, StarCraft 2, RPG Maker, World of Tanks, DayZ and League of Legends.
Mechanism of Infection
When TeslaCrypt infects a new victim, it generates a new unique Bitcoin address to receive the victim’s ransom payment and a secret key to withdraw it.
TeslaCrypt’s C&C servers are located in the Tor network. The Trojan’s version 2.0 uses two sets of keys: one set is unique within one infected system, the other is generated repeatedly each time the malicious program is re-launched in the system.
Moreover, the secret key with which user files get encrypted is not saved on the hard drive, which makes the process of decrypting the user files significantly more complicated.
Programs from TeslaCrypt malware family were observed to propagate via the Angler, Sweet Orange and Nuclear exploit kits.
Under this malware propagation mechanism, the victim visits an infected web site and the exploit’s malicious code uses browser vulnerabilities, most typically in plugins, to install the dedicated malware on the target computer.
“TeslaCrypt, a hunter of gamers, is designed to deceive and intimidate users. For example, its previous version displayed a message to the victim saying that his/her files were encrypted with the famous RSA-2048 encryption algorithm, and thus demonstrated there was no option to paying the ransom,” said Fedor Sinitsyn, Senior Malware Analyst at Kaspersky Lab.
“In reality, the cybercriminals did not use this algorithm. In its latest modification, TeslaCrypt convinces victims they are dealing with CryptoWall – once the latter encrypts user files, there is no way to have them decrypted. However, all links lead to a TeslaCrypt server – apparently, the malware authors have no intention of giving their victims’ money away to a competitor”, Sinitsyn added.
Recommendations to users
- Create backup copies of all your important files on a regular basis. Copies should be kept on media that are physically disconnected immediately after the backup copying is completed.
- It is crucially important to update your software in a timely fashion, especially the web browser and its plugins.
- Should a malicious program still land on your system, it will be best addressed by the latest version of a security product with updated databases and activated security modules.
Kaspersky Lab’s products detect this malicious program as Trojan-Ransom.Win32.Bitman.tk and successfully protect users against this threat. In addition, a Cryptomalware Countermeasure Subsystem is implemented in Kaspersky Lab’s solutions.
This registers activity when suspicious applications attempt to open a user’s personal files and immediately makes local protected backup copies of them. If the application is then judged to be malicious, it automatically rollbacks unsolicited changes by replacing those files with copies. In this way, users are protected from yet unknown cryptomalware.
Kaspersky Lab works hard to protect users of Internet against ransomware. In April in partnership with The National High Tech Crime Unit of the Netherlands the company launched The Ransomware Decryptor website.











No comments: